本文实例讲述了Yii2的XSS攻击防范策略。分享给大家供大家参考,具体如下:
XSS 漏洞修复
原则: 不相信客户输入的数据
注意: 攻击代码不一定在<script></script>中
① 将重要的cookie标记为http only, 这样的话Javascript 中的document.cookie语句就不能获取到cookie了.
② 只允许用户输入我们期望的数据。 例如: 年龄的textbox中,只允许用户输入数字。 而数字之外的字符都过滤掉。
③ 对数据进行Html Encode 处理
④ 过滤或移除特殊的Html标签, 例如: script, iframe , < for <, > for >, " for
⑤ 过滤JavaScript 事件的标签。例如 "onclick=", "onfocus" 等等。
Yii中的XSS防范
<?php echo CHtml::encode($user->name) ?>
此方法的源码:
/**
* Encodes special characters into HTML entities.
* The [[\yii\base\Application::charset|application charset]] will be used for encoding.
* @param string $content the content to be encoded
* @param boolean $doubleEncode whether to encode HTML entities in `$content`. If false,
* HTML entities in `$content` will not be further encoded.
* @return string the encoded content
* @see decode()
* @see http://www.php.net/manual/en/function.htmlspecialchars.php
*/
public static function encode($content, $doubleEncode = true)
{
return htmlspecialchars($content, ENT_QUOTES | ENT_SUBSTITUTE, Yii::$app->charset, $doubleEncode);
}
htmlspecialchars & htmlentities & urlencode 三者的区别:
http://php.net/manual/zh/function.htmlspecialchars.php
http://php.net/manual/zh/function.htmlentities.php
http://cn2.php.net/manual/zh/function.urlencode.php
Available flags constants
Constant NameDescription
ENT_COMPATWill convert double-quotes and leave single-quotes alone.
ENT_QUOTESWill convert both double and single quotes.
ENT_NOQUOTESWill leave both double and single quotes unconverted.
ENT_IGNORESilently discard invalid code unit sequences instead of returning an empty string. Using this flag is discouraged as it » may have security implications.
ENT_SUBSTITUTEReplace invalid code unit sequences with a Unicode Replacement Character U+FFFD (UTF-8) or &#FFFD; (otherwise) instead of returning an empty string.
ENT_DISALLOWEDReplace invalid code points for the given document type with a Unicode Replacement Character U+FFFD (UTF-8) or &#FFFD; (otherwise) instead of leaving them as is. This may be useful, for instance, to ensure the well-formedness of XML documents with embedded external content.
ENT_HTML401Handle code as HTML 4.01.
ENT_XML1Handle code as XML 1.
ENT_XHTMLHandle code as XHTML.
ENT_HTML5Handle code as HTML 5.
htmlspecialchars
Convert special characters to HTML entities
string htmlspecialchars (
string $string
[, int $flags = ENT_COMPAT | ENT_HTML401
[, string $encoding = ini_get("default_charset")
[, bool $double_encode = true ]
]
]
)
The translations performed are:
& (ampersand) becomes &
" (double quote) becomes " when ENT_NOQUOTES is not set.
' (single quote) becomes ' (or ') only when ENT_QUOTES is set.
< (less than) becomes <
> (greater than) becomes >
<?php
$new = htmlspecialchars("<a rel="nofollow noopener noreferrer" href='test'>Test</a>", ENT_QUOTES);
echo $new; // <a rel="nofollow noopener noreferrer" href='test'>Test</a>
?>
htmlentities
Convert all applicable characters to HTML entities
string htmlentities (
string $string
[, int $flags = ENT_COMPAT | ENT_HTML401
[, string $encoding = ini_get("default_charset")
[, bool $double_encode = true ]
]
]
)
<?php $str = "A 'quote' is <b>bold</b>"; // Outputs: A 'quote' is <b>bold</b> echo htmlentities($str); // Outputs: A 'quote' is <b>bold</b> echo htmlentities($str, ENT_QUOTES); ?>
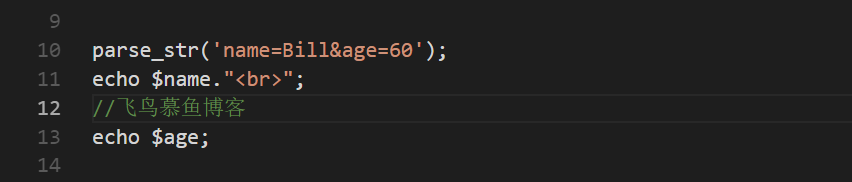
urlencode
URL 编码是为了符合url的规范。因为在标准的url规范中中文和很多的字符是不允许出现在url中的。
例如在baidu中搜索"测试汉字"。 URL会变成
http://www.baidu.com/s?wd=%B2%E2%CA%D4%BA%BA%D7%D6&rsv_bp=0&rsv_spt=3&inputT=7477
所谓URL编码就是: 把所有非字母数字字符都将被替换成百分号(%)后跟两位十六进制数,空格则编码为加号(+)
此字符串中除了 -_. 之外的所有非字母数字字符都将被替换成百分号(%)后跟两位十六进制数,空格则编码为加号(+)。此编码与 WWW 表单 POST 数据的编码方式是一样的,同时与 application/x-www-form-urlencoded 的媒体类型编码方式一样。由于历史原因,此编码在将空格编码为加号(+)方面与 RFC1738 编码(参见 rawurlencode())不同。
<?php echo '<a rel="nofollow noopener noreferrer" href="mycgi?foo=', urlencode($userinput), '">'; ?>
<?php $query_string = 'foo=' . urlencode($foo) . '&bar=' . urlencode($bar); echo '<a rel="nofollow noopener noreferrer" href="mycgi?' . htmlentities($query_string) . '">'; ?>
希望本文所述对大家基于Yii框架的PHP程序设计有所帮助。
以上就是Yii2的XSS攻击防范策略分析。有些事情只能做给自己看,做给别人看的是表演。更多关于Yii2的XSS攻击防范策略分析请关注haodaima.com其它相关文章!